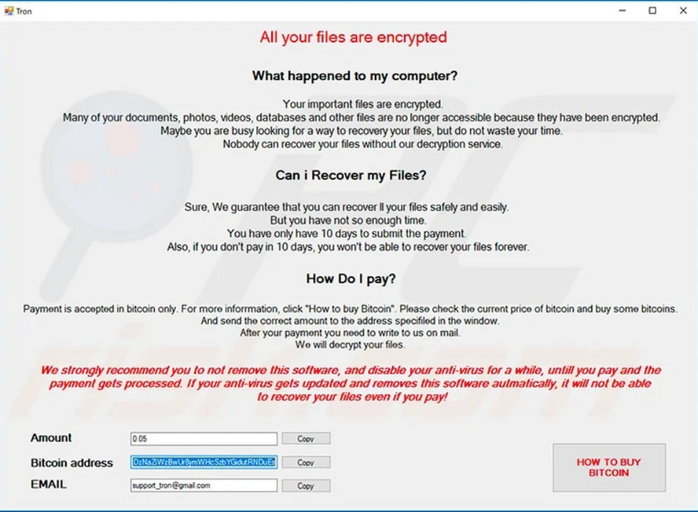
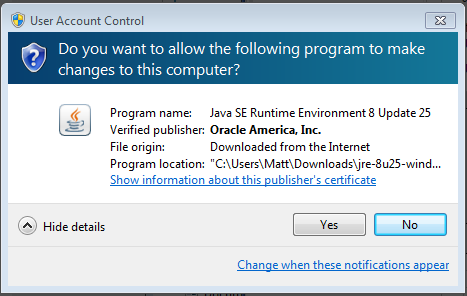
Example of 2025 trojan horse attack
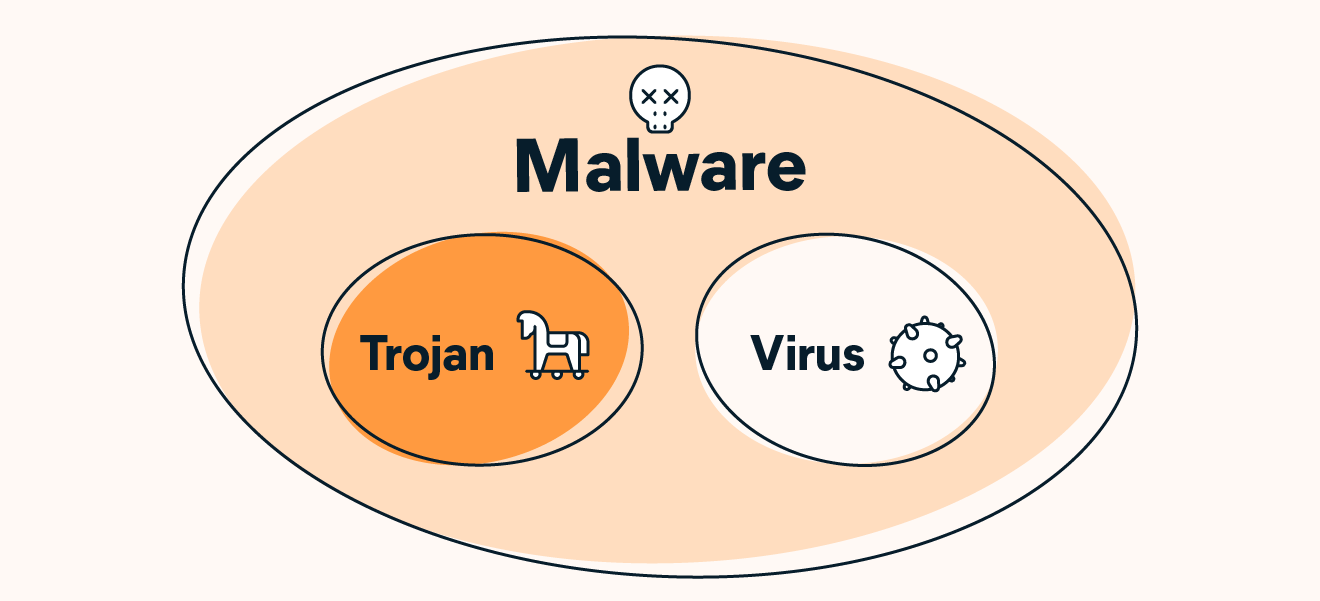
Example of 2025 trojan horse attack, What Is a Trojan a Virus or Malware How Does It Work Avast 2025
$0 today, followed by 3 monthly payments of $12.33, interest free. Read More
Example of 2025 trojan horse attack
What Is a Trojan a Virus or Malware How Does It Work Avast
What Is a Trojan Horse in Computer Terms InfoSec Insights
Trojan Horse Meaning Examples Prevention
Placeholder Trojan Writing a Malware Software
Personal Protection Against the Trojan Horse All About Trojan
What is a Trojan horse attack Shiksha Online
carnot.org
Product Name: Example of 2025 trojan horse attackWhat is a Trojan Horse Virus Types Prevention in 2024 2025, Trojan Horse Meaning Examples Prevention 2025, Trojan Horse Virus Examples How to Defend Yourself 2025, What is a Trojan Virus Trojan Horse Malware Imperva 2025, The Infamous Trojan Horse Virus What it is What it does Web 2025, What Is a Trojan Horse in Computer Terms InfoSec Insights 2025, What Is a Trojan a Virus or Malware How Does It Work Avast 2025, What Is a Trojan Horse in Computer Terms InfoSec Insights 2025, Trojan Horse Meaning Examples Prevention 2025, Placeholder Trojan Writing a Malware Software 2025, Personal Protection Against the Trojan Horse All About Trojan 2025, What is a Trojan horse attack Shiksha Online 2025, What is Trojan Horse Malware and how can you avoid it 2025, Placeholder Trojan Writing a Malware Software 2025, What is a Trojan Horse Virus Definition Examples Removal Options Video 2025, What is a Trojan Horse Virus Types Prevention in 2024 2025, Malware Based Phishing Attacks 101 What is Malware Phishing 2025, Different Examples of a Trojan Horse Types of Trojan Horse 2025, What Is a Trojan Horse in Computer Terms InfoSec Insights 2025, Trojan Horse The Basics XtraWeb 2025, What is Trojan Horse Virus Protect Yourself Against Trojan Viruses 2025, What is a Trojan Horse Virus Types and How to Remove it 2025, AIDS Trojan horse Wikipedia 2025, No money but Pony From a mail to a trojan horse Malwarebytes Labs 2025, Trojan Horse Virus Trojan Horse Malware What is a Trojan Virus 2025, What are Trojan Viruses and How Do These Threats Work Top Cloud 2025, How trojan malware is evolving to survive and evade cybersecurity 2025, What is a Trojan horse attack Shiksha Online 2025, What Is a Trojan Virus Definition Types Prevention Tips 2025, What Is a Trojan Horse Trojan Virus and Malware Explained Fortinet 2025, Your System Has Been Hacked With A Trojan Virus Email Scam 2025, What is a Trojan Horse U.S. News 2025, My Trojan Captured All Your Private Information Email Scam 2025, Storm Worm Wikipedia 2025, The Trojan Horse Story Context in Popular Culture Study 2025.
-
Next Day Delivery by DPD
Find out more
Order by 9pm (excludes Public holidays)
$11.99
-
Express Delivery - 48 Hours
Find out more
Order by 9pm (excludes Public holidays)
$9.99
-
Standard Delivery $6.99 Find out more
Delivered within 3 - 7 days (excludes Public holidays).
-
Store Delivery $6.99 Find out more
Delivered to your chosen store within 3-7 days
Spend over $400 (excluding delivery charge) to get a $20 voucher to spend in-store -
International Delivery Find out more
International Delivery is available for this product. The cost and delivery time depend on the country.
You can now return your online order in a few easy steps. Select your preferred tracked returns service. We have print at home, paperless and collection options available.
You have 28 days to return your order from the date it’s delivered. Exclusions apply.
View our full Returns and Exchanges information.
Our extended Christmas returns policy runs from 28th October until 5th January 2025, all items purchased online during this time can be returned for a full refund.
Find similar items here:
Example of 2025 trojan horse attack
- example of trojan horse attack
- examples of electroplated products
- examples of electroplating in daily life
- examples of electroplating in industry
- examples of electroplating objects
- examples of game consoles
- examples of linen
- examples of pumps
- examples of thermometer
- examples of trojan horse virus attacks